I recently wrote a pdf about wallet security, and added some items to it today. Below is a copy/paste from the original document, and I will post a download link at the end so you can download the pdf (since the allowed attachment size is so small it’s basically useless LOL)
[center]Protect Your Wallets!
A Guide to Creating a Fortress of Encryption to Safely Secure Your Coins
(and other stuff too)
[/center]
Encrypting your data these days is of the utmost importance. Considering the day and age we live in, not having your data encrypted is like walking around in public wearing a T-shirt that has your social security number, date of birth, bank account numbers, credit card numbers, and your mother’s maiden name on it. Not smart!
Now, it is important to remember that nothing is ever 100% safe. For all we know, DARPA might know how to crack RSA-4096 or SHA-512. However, I think that is unlikely, and besides, I’m sure DARPA doesn’t care about our silly little coin wallets. They have bigger fish to fry.
So, assuming the government isn’t after you personally, our main focus is to protect ourselves from common thieves and cyber criminals. Like I said before, nothing is 100% safe, but there’s no point in making things easier on anyone who is trying to steal your crypto currency. All it takes is about 30 minutes on your part to take some very basic precautions.
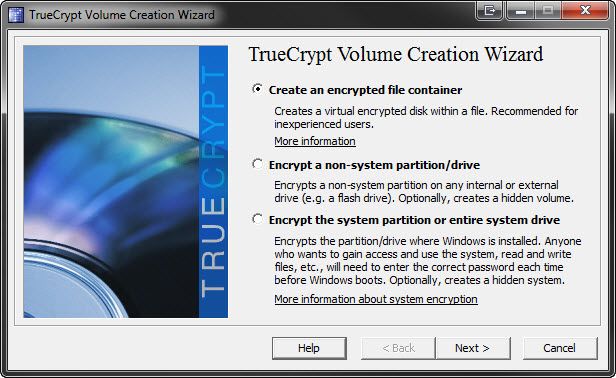
Firstly, you will need to obtain two free and open source programs, KeePass, and TrueCrypt (if you use Last Pass then you do not need KeePass).
http://keepass.info/
http://www.truecrypt.org/
Take some time to familiarize yourself with them. There is documentation available as well as tutorials. For TrueCrypt, visit http://www.truecrypt.org/docs/ and read through everything so that you have a good idea what TrueCrypt does, how it does it, and how to use it. If you have never used a password manager before, I recommend using KeyPass to create one password for one of your email accounts (because password recovery/resetting is simple and painless in the event that you manage to fuck something up). Use KeyPass to access your email account for as long as you need to until you feel comfortable using it. Once you feel comfortable with it, then start using it for everything else. I know it seems a little silly and elementary, but I really want to emphasize how important it is to be 100% comfortable using KeyPass. Remember, if you safeguard your wallets with TrueCrypt and KeyPass and you somehow screw everything up and lose access to your passwords, you will probably lose your coins forever. Don’t let this scare you though, just let it remind you to take this seriously, even if it seems a little silly taking baby steps until you’re ready to jump in with both feet.
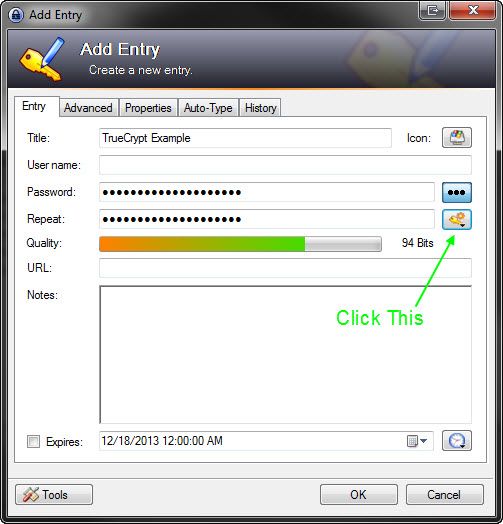
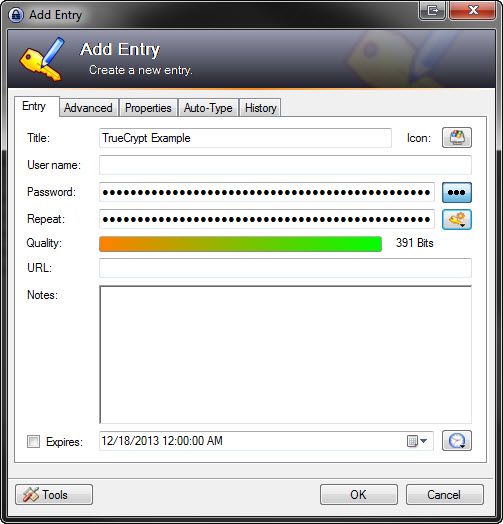
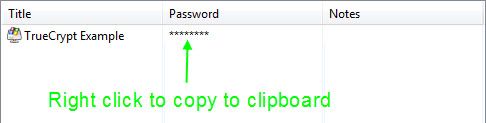
When it comes time to create a password for your TrueCrypt volume, go to KeyPass and create a new entry.
Click the button above and select “Open Password Generator”. Make it look like this and press OK.
This will bring you back to the previous window. Press OK.
Continued Below…